When you read different VPN reviews, you’ll probably notice the same thing coming up again and again: whether a VPN has passed an independent third-party audit.
But what exactly is a VPN audit? How is it carried out? And does an audited VPN always mean it is safe, private, or truly no-logs? In this article, I’ll walk you through all of it.
Table of Contents
What Is a VPN Audit?
A VPN audit is basically a review of a VPN provider’s claims about privacy, security, infrastructure, or logging practices.
In simple terms, when a VPN says things like “we keep no logs”, “we protect your privacy”, or “our systems are secure”, an audit is a way to check whether those claims actually match how the service is set up and run.
Strictly speaking, VPN audits can include both internal checks and external audits. But when reviewers, privacy experts, and the media talk about a “VPN audit”, they are usually referring to an independent third-party audit. That is also the kind of audit this article mainly focuses on, because it is the type most often used as a trust signal in the VPN industry.
There are two other things worth keeping in mind here. First, VPN audits usually have a defined scope. Some focus on no-logs claims, some look at server infrastructure and security controls, while others examine apps, source code, or broader compliance practices. So, not all VPN audits mean the same thing. Second, an audit is usually a point-in-time review. It reflects what the auditor examined at that time, not a permanent guarantee that every part of the service will always remain the same.
Common Types of VPN Audits
VPN audits often cover very different areas. Some are designed to test privacy claims, while others focus on infrastructure, apps, protocols, or broader organisational controls.
Here are five of the main types found in the VPN industry.

1) No-Logs, Infrastructure, and Privacy Controls Audits
This is the type of audit most people mean when they talk about a VPN audit.
Its main purpose is to assess whether a provider’s privacy and no-logs claims are credible. In simple terms, it tries to answer the question users care about most: Does the VPN really not collect the data it says, or are those claims mostly marketing?
To answer that, auditors usually look beyond the privacy policy itself. They will review the technical environment behind the service, including server configurations, logging pathways, access controls, and supporting IT operations. The goal is to determine whether the provider’s systems and processes actually support its stated no-logs position.
This type of work is often carried out by large, famous assurance firms such as Deloitte or KPMG. It is commonly performed under assurance frameworks such as ISAE 3000 or ISAE 3000 (Revised), which comes from the IAASB and is specifically for assurance engagements outside standard financial statement audits.
The IAASB first released the older version of ISAE 3000, and later made significant updates, mainly clarifying, tightening, and making some details more actionable. Therefore, the new version is called ISAE 3000 (Revised), and they are not two different standards. ISAE 3000 (Revised) applies to assurance projects with reporting dates on or after December 15, 2015.
2) App and Client Source Code Audits
Unlike the previous one, this type focuses on whether the VPN application itself is secure and trustworthy. These audits may cover desktop clients, mobile apps, browser extensions, or other user-facing software.
Auditors typically examine the source code or implementation for weaknesses such as security flaws, data leaks, unsafe permissions, poor handling of sensitive information, or other risks that could affect users directly.
This kind of work is usually carried out by specialist cybersecurity firms rather than accounting firms. One well-known example is Cure53, which explicitly lists code audits, white-box tests, and black-box penetration tests as part of its services.
3) Protocol Audit
Some VPN providers also commission audits of the VPN protocols they use, especially if they have developed their own protocol or place a strong emphasis on a specific one.
A protocol audit looks at the underlying technology that handles secure connections between the user and the VPN server. It may review things like encryption implementation, key exchange, handshake logic, session handling, memory safety, and other technical details that affect how secure the protocol really is.
4) Penetration Tests and Security Assessments
A penetration test or security assessment is usually designed to identify weaknesses that could be exploited by an attacker.
Depending on the engagement, this may involve testing apps, websites, APIs, account systems, internal services, backend infrastructure, or other parts of the VPN environment. The focus is on finding vulnerabilities, misconfigurations, and realistic attack paths before malicious actors do.
So, different from a no-logs audit, a penetration test looks for exploitable weaknesses, while a no-logs audit is primarily concerned with whether privacy claims are operationally credible.
5) SOC 2 and Broader Control Audits
This last category is broader and more organisational. Instead of focusing on one app, one protocol, or one no-logs claim, it looks at the company’s overall control environment. The concern it helps address is: Is this provider operating in a structured, responsible, and well-controlled way behind the scenes?
That can include things like access management, system monitoring, risk handling, internal processes, confidentiality controls, and privacy-related controls at the company level. A common example is SOC 2, which the AICPA defines as an examination of controls relevant to security, availability, processing integrity, confidentiality, or privacy.
In a word, when you see a VPN says it has been “audited”, instead of stopping at the word itself, it’s better to know “what kind of audit was it, what did it actually examine, and what doubt was it meant to address”.
How Is a VPN Audit Usually Conducted?
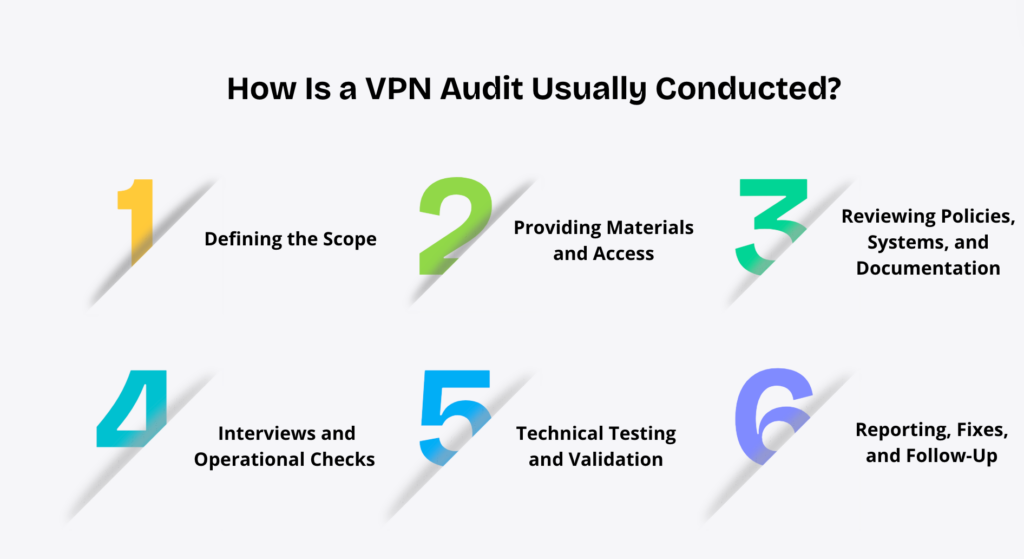
1) Defining the Scope
The first step is deciding what the audit is actually about. Is it a review of no-logs declarations, a specific app, a particular protocol, a server set, or organizational controls?
2) Providing Materials and Access
Once the scope is defined, the provider usually needs to give the auditors the materials and access required for the review.
Depending on the type of audit, this may include privacy policies, internal documentation, technical architecture, server or infrastructure information, source code, test accounts, system configurations, or access to relevant environments.
3) Reviewing Policies, Systems, and Documentation
Once the necessary materials and access are in place, the audit usually moves into a review stage.
4) Interviews and Operational Checks
A VPN audit is not only about reading documents. In many cases, auditors also speak with the teams involved.
That can include asking how systems are managed, how logging is handled, who has access to production environments, how changes are deployed, or how internal controls work in practice.
5) Technical Testing and Validation
This stage may involve reviewing source code, checking server configuration, testing apps, examining protocol implementation, or looking for vulnerabilities and misconfigurations. In other words, this is where the auditor goes beyond what the provider says and starts checking how the service actually works in practice.
6) Reporting, Fixes, and Follow-Up
After the review and testing stages, the auditor usually issues a final report or conclusion. Depending on the type of audit, this may confirm whether certain claims were supported, or highlight technical issues, weaknesses, and recommendations.
If problems are found, the provider may fix them and go through follow-up verification. And because systems and operations can change over time, many VPN providers repeat audits regularly instead of treating them as a one-time exercise.
What Does a VPN Audit Report Tell You?
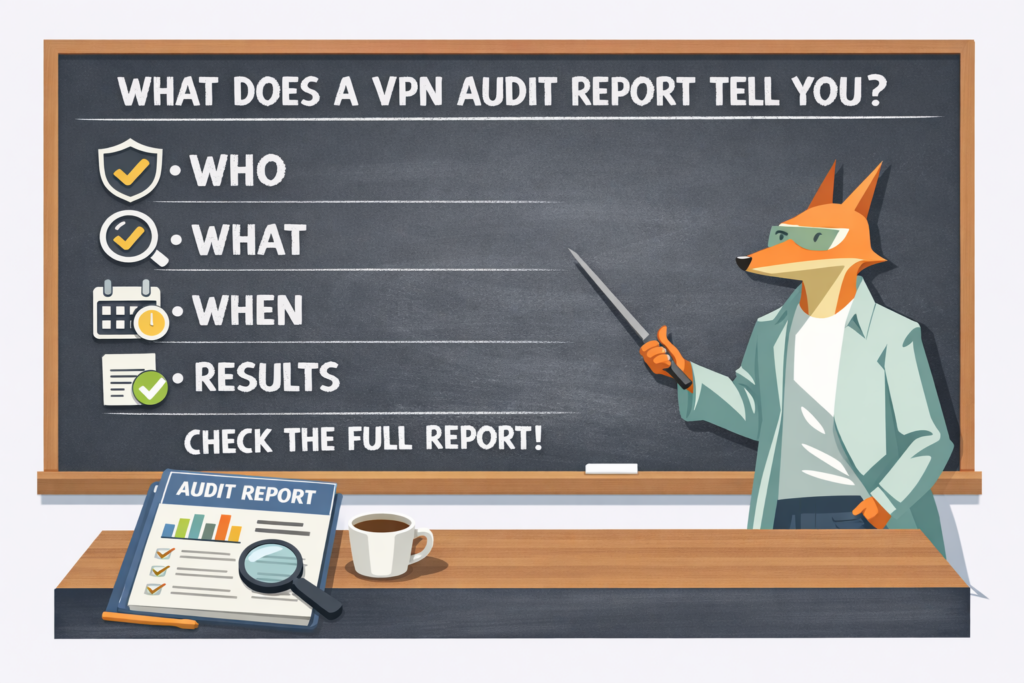
A VPN audit report is usually quite structured. In most cases, it covers the audit methodology and scope, the components reviewed, the findings, any recommendations, and the final assurance statement.
For users who are not familiar with the technical side, you don’t need to go through every detail. The most important things to focus on are the following:
Lastly, how much detail is disclosed still matters. This helps you judge how transparent the provider is about the audit report. If a provider shares almost nothing beyond a broad claim that it has “passed an audit”, you should be more cautious.
Why Third-Party VPN Audits Matter for You
A VPN can claim everything it wants. But as a user, you probably have no way to check any of that yourself. That is why VPN audits matter. They give you something more reliable to look at than marketing claims alone.
This is also why audits are mentioned so often in VPN reviews. Reviewers know that privacy and security promises are hard to verify from the outside, so an independent audit can serve as an extra trust signal.
The former is more consumer-oriented, focusing on whether a VPN is easy to use and worth recommending; the latter is more verification-oriented, focusing on whether a claim, system, or control has undergone independent and professional scrutiny. Simply put, reviews answer “How well does this VPN work?”, while audits answer “Has a certain claim about this VPN been verified?”
Especially For Free VPN Users
This matters even more when it comes to free VPNs. Many users have heard the phrase, “If a product is free, you are the product.” To be honest, only a small number of free VPNs actually profit by selling user data, and this is more often seen when the company behind the service is focused on marketing, traffic, or advertising rather than VPN products themselves.
By contrast, a free VPN that is genuinely built around the VPN product usually makes money in other ways. Some rely on ads, while others use a freemium model, offering a free version and encouraging users to upgrade for more features over time to support long-term growth.
Still, simply saying that is not enough. That is why independent audits matter so much for free VPN providers. They are one of the clearest ways to show users that the service’s privacy claims are not just marketing.
Is X-VPN Audited by a Third Party?

Yes, X-VPN is currently undergoing an independent third-party audit. The audit falls under No-Logs, Infrastructure, and Privacy Controls Audits and is being conducted under ISAE 3000 (Revised). The results are expected to be disclosed soon.
But this is only the beginning. To maintain a high level of transparency, X-VPN also plans to carry out other types of audits in the future, including the SOC 2 audits.
More importantly, X-VPN intends to make auditing a regular and ongoing practice, rather than treating it as a one-time milestone. Our goal is simple: to make sure every user can use X-VPN with confidence.
Beyond Audits: How X-VPN Supports Privacy
At X-VPN, user privacy and peace of mind have always been a top priority. That is exactly why we believe trust should not rely on claims alone. Audits are an important part of that, but they are only one part.
To make our privacy approach more transparent and easier for users to understand, X-VPN also continues to invest in other areas. For example, we maintain a transparency report to disclose information such as DMCA requests and bug bounty updates.
At the product level, X-VPN also takes a more practical approach to privacy and security. We support widely trusted open-source protocols such as WireGuard and OpenVPN, giving users more visibility into the technologies behind their VPN connections. At the same time, all X-VPN servers are built on a RAM-only architecture, which helps reduce the risk of data being stored long-term on physical disks.
Privacy you can trust. Security you can feel.
Strong encryption with AES-256 and post-quantum encryption
Advanced features like double VPN and private DNS
Built-in tools like Ad Blocker and Dark Web Monitor
Final Thoughts
In the end, a VPN audit matters because it gives users something more solid than promises alone. But it is also important to stay realistic. An audit is not a magic stamp, and it does not automatically prove that a VPN is perfect forever. What really matters is what was audited, how it was audited, and what the result actually supports.
For X-VPN, this is exactly how we see it too. Independent audits are an important part of building trust, but they are only one part. Transparency reports, open protocols, RAM-only servers, and ongoing privacy and security improvements all matter as well.
FAQs
What does a VPN audit actually prove?
It demonstrates that:
Within the scope of the audit, certain privacy, security, or no-logs practices claimed by the VPN have been independently verified by a third party and are consistent with actual system configurations, operational processes, or controls.
Is an audited VPN always safe?
No. An audit improves confidence, but it does not eliminate risk. A VPN can still have weaknesses outside the audit scope, change its systems later, or face new threats after the audit was completed.
Does a VPN audit mean no logs?
No. Even if the audit was specifically designed to verify no-logs claims or privacy controls, the audit usually shows: the provider’s actual systems, processes, and controls are broadly consistent with the way it describes its no-logs approach.
So the key is not just whether it was audited, but: what the audit actually covered, and how the provider defines and presents its no-logs claim in the first place.
How often should a VPN be audited?
There is no universal rule, but one audit should never be treated as enough forever. From a user’s point of view, regular audits are a much stronger signal, because VPN apps, infrastructure, internal processes, and logging controls can all change over time.
Where Can You Find a VPN Audit Report?
You can usually find it on the provider’s official website, such as the Trust Center or related blog posts. In some cases, the full report may only be available after logging into your account, depending on the auditor’s requirements. Since every VPN handles disclosure differently, contacting customer support is also a practical option.
Is X-VPN independently audited?
Yes. X-VPN is currently undergoing an independent no-logs audit. And the results are expected to be disclosed soon.



